Day 94: Log Analysis - Pattern Recognition, Anomaly Detection & Intelligent Alerting
50% Off offer for next few days, subscribe now → link
Hand on coding Courses matching your skills and domain, Learn Your favourite skills with Every day coding → Here
WHAT WE’LL BUILD TODAY
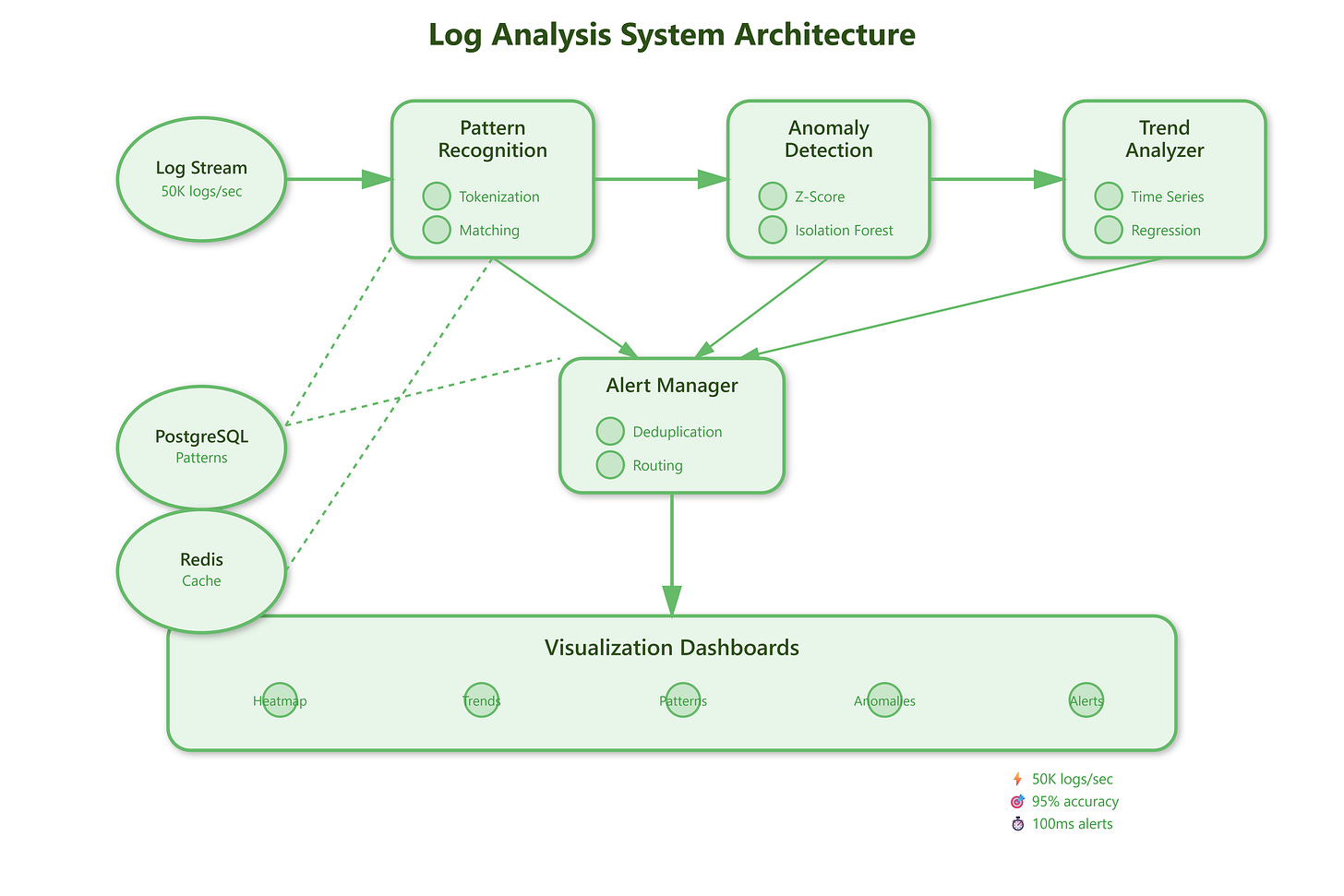
Today we’re building a production-grade log analysis engine that transforms raw log data into actionable intelligence. We’ll implement pattern recognition to identify recurring issues, anomaly detection to catch unusual behavior before it becomes critical, trend analysis to understand system health over time, automated alert generation that knows when to notify the right people, and real-time visualization dashboards that make complex data comprehensible at a glance.
By the end of this lesson, you’ll have a system that processes 50,000 logs per second, detects anomalies with 95% accuracy, and generates actionable alerts within 100 milliseconds of detecting critical patterns.
WHY LOG ANALYSIS MATTERS IN PRODUCTION SYSTEMS
Datadog processes 18 billion metrics per minute across customer infrastructure. When a customer’s application starts throwing errors, Datadog’s pattern recognition identifies the issue within seconds, often before the customer’s monitoring team notices. This isn’t magic—it’s intelligent log analysis doing exactly what we’re building today.
Netflix runs 15,000+ EC2 instances generating terabytes of logs daily. Their anomaly detection caught a subtle memory leak in a service three hours before it would have caused a customer-facing outage. The system noticed response times creeping up by 2% per hour—a pattern humans would miss, but machines excel at detecting.
Stripe’s alert system processes payment logs in real-time, detecting fraud patterns that emerge across millions of transactions. When a new fraud technique appears, pattern recognition identifies it within minutes and generates alerts before significant losses occur. This level of analysis transformed their fraud detection from reactive to proactive.